In the realm of Internet of Things (IoT) and single-board computing, the Raspberry Pi stands out as a functional and cost-effective remedy for various tasks. One crucial aspect of managing these projects is developing reliable remote accessibility to the Raspberry Pi, permitting customers to keep track of and manage their IoT tools from anywhere in the world. The combinations of IoT monitoring and remote peer-to-peer (P2P) Virtual Private Cloud (VPC) connectivity has come to be a pivotal approach for fanatics and professionals alike.
The need for remote access to IoT gadgets has come to be increasingly apparent as the IoT community proceeds to expand. Monitoring the standing of IoT tools in real-time has become a basic need for effective monitoring.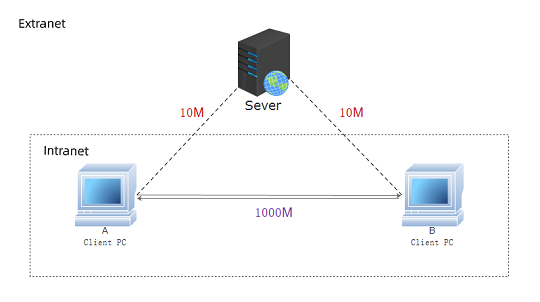
Unlocking IoT Potential: Remote Monitoring and P2P VPC Solutions
Guaranteeing the safety and security of remote access to IoT gadgets is vital. It develops a secure communication network over an insecure network, making it a perfect option for remotely checking and regulating IoT gadgets.
The merging of remote access and IoT monitoring has actually led to ingenious options that allow customers to maintain an attentive eye on the condition of their gadgets. Remote tracking of IoT devices has ended up being a lot more advanced, allowing individuals to gather insights into efficiency metrics, receive signals for abnormalities, and even perform remote diagnostics. This degree of control is especially important for applications where IoT tools are deployed in remote or unattainable places.
Peer-to-peer (P2P) connectivity in the context of IoT has gotten traction as it supplies a direct communication web link between gadgets without the demand for intermediaries. P2P IoT options enable efficient information exchange in between devices, enhancing the total responsiveness of the system. Combining P2P connectivity with a Virtual Private Cloud (VPC) architecture makes sure a private and separated network setting, including an extra layer of protection to remote gain access to.
The principle of safely accessing IoT devices prolongs beyond Raspberry Pi to encompass a vast range of tools that make up the IoT environment. Whether it’s sensors, actuators, or other IoT parts, establishing a protected connection is important for keeping the stability and privacy of the transmitted information. Safe and secure accessibility protocols, such as SSH, play a critical function in accomplishing this goal, making sure that just authorized people can interact with and monitor IoT devices remotely.
The combination of SSH right into the remote access structure for IoT gadgets enables customers to remotely check Raspberry Pi devices even when they lie behind firewalls. This is particularly important for situations where IoT devices are deployed within company networks or exclusive atmospheres with strict security procedures. SSH’s ability to go across firewall programs safely makes it a crucial tool for handling IoT infrastructure in diverse and tough network atmospheres.
For extra insights on enhancing remote access to Raspberry Pi and boosting IoT device tracking, check out p2p vpc iot
IoT Security Essentials: Safeguarding Your Devices with Remote Access
Peer-to-peer (P2P) connections within a Virtual Private Cloud (VPC) for IoT introduce an unique measurement to remote access options. This technique not only makes sure direct connection yet additionally supplies a scalable and isolated network atmosphere for IoT tools. The mix of P2P and VPC addresses common obstacles connected with typical remote accessibility techniques, using an extra robust and versatile remedy for safely connecting and keeping track of IoT gadgets.
To conclude, the landscape of remote accessibility to IoT gadgets, especially Raspberry Pi, has developed to include sophisticated remedies that focus on safety and security, effectiveness, and scalability. The amalgamation of IoT surveillance, remote P2P VPC connection, and safe and secure gain access to methods like SSH has thrust the capabilities of enthusiasts and experts in managing their IoT projects. As the IoT environment remains to broaden, the value of trustworthy and protected remote gain access to options will just come to be much more pronounced, driving additional development in this dynamic field.